From a Stack Overflow question: “a hacked version of a Google Chrome extension I use was distributed via Chrome’s automatic extension updates. Is it possible to stop Google Chrome from automatically updating extensions?”
The answer is there’s not an easy way to disable them in Chrome. But there should be, and this post explains why. There are DIY ways to disable auto updates though (more on that later). Google should look to the rest of the industry: Firefox already offers extension-specific controls to disable automatic updating.
A “hacked version of a Google Chrome extension”: such a common story.
There is a whole industry around buying/selling popular Chrome extensions and then monetizing the users by selling their data. Here are some links that highlight the problem: “I Sold a Chrome Extension but it was a bad decision” [ -> because the buyer inserted adware into the plugin]. “‘Particle’ Chrome Extension Sold to New Dev Who Immediately Turns It Into Adware” [ -> the new “owner” had done this to several extensions]. “I found your data. It’s for sale” [ -> A terrific Washington Post deep dive on extensions that spy on users: “Some extensions have a side hustle in spying. From a privileged perch in your browser, they pass information about where you surf and what you view into a murky data economy.”] “5 Shady Google Chrome Extensions You Should Uninstall ASAP” [ -> “Once-legitimate extensions are often sold to malicious companies, who then use them to make money by selling your data.”] “Chrome and Firefox pull an extension called Stylish that sold to SimilarWeb in 2017, had roughly 2M users, and was found collecting users’ web usage histories“.
As you can see ^, it’s a well-reported phenomenon: many extension developers trade their users’ privacy and security for bags of cash. Because extensions quietly and automatically update, users aren’t alerted when their extensions’ code changes.
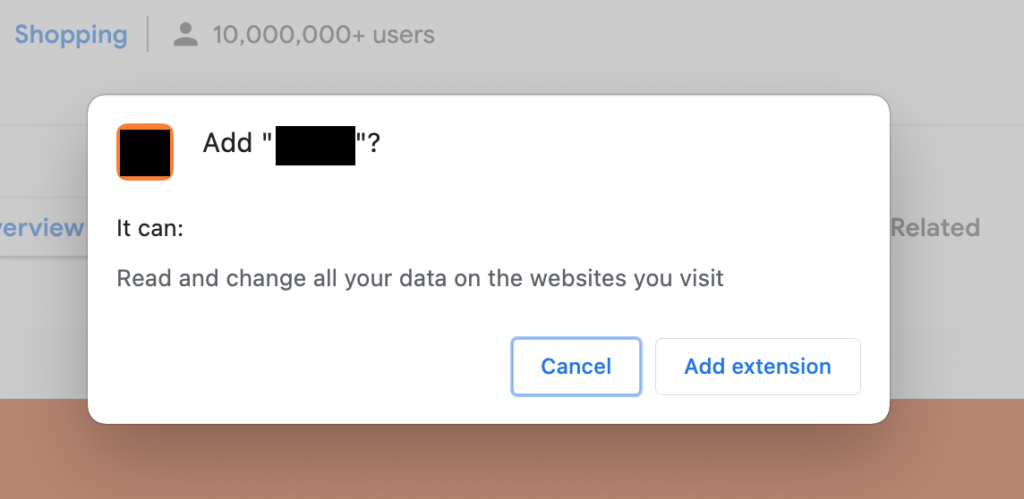
The stakes for extensions that go rogue are very high, because they typically ask for and receive sweeping permissions.
Some developers, instead of outright selling their extension, simply add a 3rd-party SDK to the code of the extension (in exchange for $$$ from a “marketing” agency). Again, extensions going “rogue” happens a lot, as developers of popular browser extensions get approached and tempted by opportunists and bad actors. Just judging by the sheer number of installed malicious extensions written about in past year alone (with hundreds of millions of installs) (not to mention the ones that weren’t reported on) — one can appreciate the scale of the problem.
Here are just a few examples: “Avast found 28 malicious Chrome and Edge extensions with 3M+ downloads, many posing as third-party add-ons for Instagram and Facebook; 25 still remain in stores”.
– “Researchers find a cluster of 295 Chrome extensions, with more than 80M users, that inserted ads into Google and Bing results; Google is now removing some”.
– “Google removes 106 malicious Chrome extensions with 32M downloads that collected browsing history and sensitive credentials, after being alerted by researchers”.
– “Google has removed 500+ malicious Chrome extensions from its Web Store, likely affecting millions of users, that were part of a long-running ad fraud network”.
Google calls Chrome “Fast & Secure”. How secure is it though, if so many of its users get bitten by malware through its Chrome Web Store via unstoppable automatic updates?
Chrome should provide an easy way to disable automatic updates of specific extensions. There is a way to manually prevent the updates, but it’s an ugly hack (more on that later).
Why we need the ability to disable automatic updates
Chrome should let users disable auto updates for specific extensions, to freeze changes to the extension’s code. This would allay the concern that the extension could change to be malicious without the user’s knowledge.
Chrome should learn from Firefox:
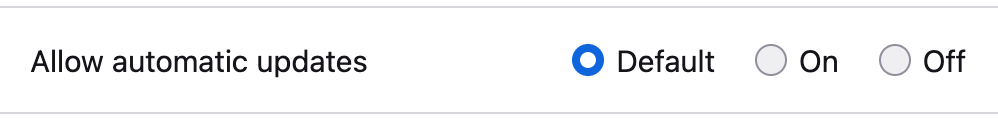
To be clear, I think Chrome should go beyond what other conventional App Stores do. Some extensions, from brands/devs you trust, should be able to keep updating automatically, while updates for other extensions are selectively paused. In other words, Chrome should let users easily turn off auto-updates for specific extensions, like Firefox does. Extensions like LastPass or 1Password or whatever (if you’re brave enough to use those in the first place) should of course be updating automatically. But Chrome should let you pause updates from extensions from less-trusted developers. [For what it’s worth, Mac’s Safari does appear to take a better approach than Chrome, treating its extensions more like apps from the app store.]
There’s a trade off here: by disabling the automatic updating of an extension, you deny that developer the ability to maliciously alter the extension. That’s good. But what if the developer wanted to push a security fix or new feature? If the browser handled this like a normal app store: users would get notifications of incoming updates and have a chance to review them. That’s what we need: properly handled incremental updates. I believe Firefox could improve in this regard as well: if I pause automatic updates for an extension, I should still get a notification when a new update arrives for it.
I have written and published a few extensions myself [1, 2, 3], for Chrome and Firefox, and (years ago) came to the conclusion that (as a user) installing extensions is supes scary. In that way, I’m kind of like the fast food worker who won’t eat at the restaurant where they work. The security model is… kind of non-existent after the user agrees to the initial permissions. For the few safeguards that are in place, extension developers are known to try to override them to make things work. As a result, I came up with my own extension hygiene practices.
How to DIY, a.k.a. Ugly Hacks
There are complicated ways to prevent extensions from auto-updating on Chrome, and they have serious shortcomings. From multi-step terminal command instructions on Mac, to registry hacks and more on Windows, to the DIY method I am about to share below, there are ways to make it happen. But all of these I consider ugly hacks. Chromeshould surface easy ways to disable auto updates in the user interface of the browser itself, with an interface that alerts users to proposed extension updates from the developer.
These days, before installing any extension, I:
- read the code of said extension to look for anything suspicious,
- create a local copy of that extension, and then
- run that local copy via Chrome’s “Load Unpacked” dev option.
After these steps, the local copy of the extension runs normally but is not susceptible to automatically updating.
As a consequence of this approach, I don’t run exceedingly complex extensions or any that “minify” or obfuscate their code; I need to be able to understand the inner workings of the plugin. I don’t recommend this process for all extensions- and some may disallow this practice via an end user licensing agreement, but it’s an important option to have, since the browser does not let us disable browser extension updates. It’s an imperfect hack, because the I don’t get notified of legit new updates to the extension. It’s incumbent upon me to manually/ periodically check for updates to that extension. Again, the browser should make toggling auto updates a formal process that’s accounted for in the browser UI.
A tool that I use to help quickly assess an extension is called Chrome Extension Viewer, which itself can be run from a local copy. It’s available on Chrome and Firefox. Below is a video of me using the tool.
So, to summarize … 1.) too many extension developers sell out their users, 2.) Chrome should let users disable auto-updates of extensions to protect themselves, 3.) if you want to take matters into your own hands and (theoretically) eliminate the concern of point #1, you can with ugly hacks.
Was any of this helpful? Please consider supporting Key Discussions by becoming a member on Patreon! Join a lively discussion on Reddit!